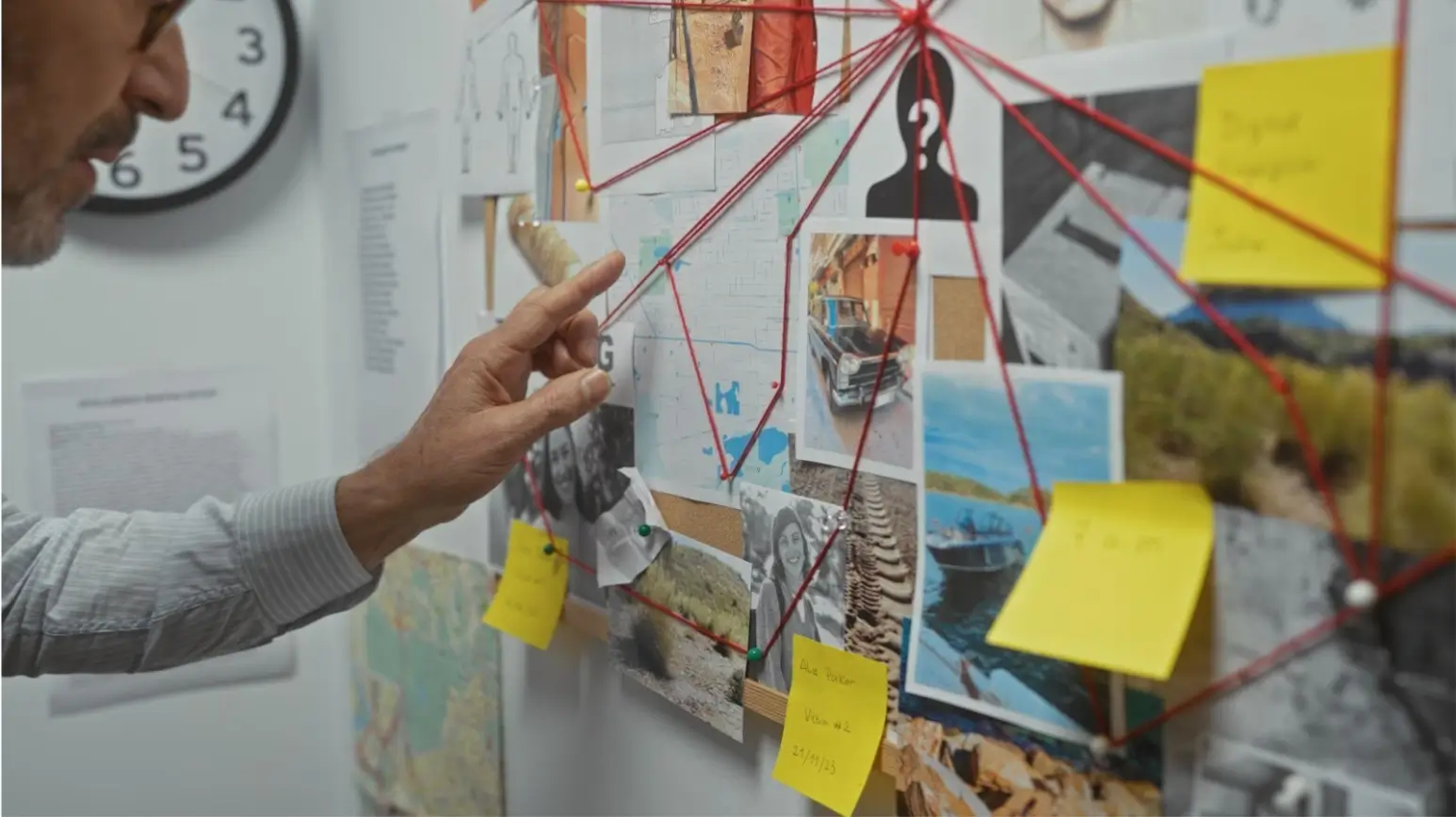
How Cybercriminals Exploit Mobile Network Weaknesses
Mobile devices have become an integral part of our daily lives. We use them to browse the Internet, do shopping, consume content, but also perform various work-related tasks. Unfortunately, unlike our computers, smartphones don’t have the same level of protection, providing an easy way into a company’s systems. During mobile hacking, a criminal will exploit … Read more