With the pervasiveness of the internet on one end, and the proliferation of threats on the other, cybersecurity is a critical component of the digital space. As a result, a quick and effective response is required to mitigate these attacks.
Report after report claims that malicious hacking is “more sophisticated than ever before.” The media wants the world to believe there are unstoppable hackers with sophisticated skills and tools coming at them at full force.
But the reality is quite different; hackers are still using the same old tools and exploiting the same weak points as they did, albeit with a few modifications.
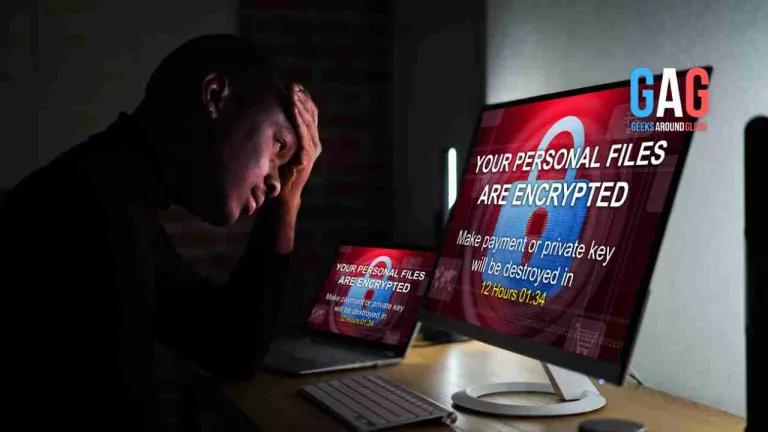
If you’re a business owner, to prevent precious data from falling into the wrong hands, you can either pay a ransom or watch your data sold to the highest bidder.
Sure, backups may save you, but once your data is stolen, rebuilding may take weeks, giving your attackers ample time to explore and exploit that data to their advantage.
While there isn’t a surefire way to make yourself fully hack-proof, there are steps you can take to decrease your chances of falling victim to a cyberattack.
- Keep track of the latest information.
The world of online hacking is constantly evolving. Your current anti-virus software may be ineffective against a virus created in a few months, so you must keep up with all of the latest developments in the global world of cyber security.
There are numerous blogs and websites you can check out that are run by professionals in cyber security, providing readers with up-to-date information on global hacking attacks.
Another step towards strengthening your understanding of cyberattacks would be through an online certification or a degree program based on cybersecurity.
Suppose you have an undergraduate degree in a technical discipline. In that case, a Master of Science in Cybersecurity can help you understand and develop the skills needed to protect yourself against internet-related threats.
- Software updates
While software updates like the ones from Microsoft are provided for free, end users may ignore or delay installing those updates due to busy schedules.
Software firms continually provide these patches to make their products more secure, and failing to install them can leave devices vulnerable to an attack, so don’t ignore them.
- Choose a strong password.
It’s pretty shocking to see well-educated experts still using passwords made up of their relatives’ names, birthdays, and so on. These passwords are easy to guess and end up leaving your information vulnerable to hackers.
Thus, ensure your password consists of a random combination of symbols and letters. Also, never reveal your password to anyone else, and change it at least once every few months.
- Keep an eye out for phishing emails and messages.
We’ve all received an email purportedly sent by a European prince or a long-lost relative promising to leave us large sums of money at some point in our lives. None of us are that lucky, and all such emails are standard phishing schemes.
Emails or messages like these are designed to entice us with tempting offers in exchange for information such as our credit card or banking numbers.
As a rule of thumb, never open an email in your inbox that is not from a trusted source, and only open emails from recognizable senders if you expect them.
If you suspect an email from a bank, get in touch with the bank before opening that email to know if it’s legit.
- Cut back on data transfers.
Transferring data from business devices to other devices is unavoidable as the number of remote employees grows. While it may appear to be secure, storing work data on personal or external devices exposes your data to hackers.
Working or collaborating with an experienced cybersecurity provider will assist in determining which devices or endpoints are vulnerable and how to protect them best.
- Use firewalls
In the case of e-commerce, your website host will have a firewall built into your server. Aside from that, you should consider purchasing one for your computer.
Many security plug-ins include a built-in firewall, so when an attack is launched against your computer, you will receive a message, and the firewall will prevent any unauthorized access.
- Keep your devices secure.
Suppose your mobile device is left unattended, stolen, or lost. In that case, sensitive information like messages, pictures, or bank information can be stolen. It would be best to secure your devices with the following practices:
- Don’t install applications that aren’t from reputable sources
- Register your fingerprints to make the device secure
- Disable Bluetooth when not in use
- Enable remote wiping functions and locking
Conclusion
Cyber security is a critical consideration in today’s digital world. With so much of our personal information at our fingertips, there are always other internet-related risks to be aware of.
However, by learning how to deal with cyber security threats, you increase the chances of keeping your data safe from prying eyes.