Modern realities of electronic workflows require quite effective methods of protection. We are talking not only about ensuring secure access to data, but also about guaranteeing the protection of the entire system in general.
Since electronic workflows have moved to a new level, various hackers and scammers who want to commit crimes have become more active. Therefore, we have selected 5 affordable and effective methods to protect electronic workflows and the overall work system in order to avoid negative consequences.
Protection of Electronic Documents
Now electronic documents are the most convenient and simplified version of bureaucracy. They are much easier to format, create, and process. As a result, it speeds up the workflow and saves time.
But the security of electronic documents is an important aspect of working with them, especially if they end up on the Internet. One of the main tools to protect against plagiarism or use by third parties is to add a watermark to all documents. This is not a difficult task if you know how to convert pdf to jpg, but there are also companies that can do it for you. Watermarking is the most straightforward and reliable electronic workflow protection mechanism.
Also, one of the available ways to protect documents is to encrypt them or use blockchain technologies. The cost of time and resources for this is more than using a watermark, but it all depends on your capabilities and goals.
The main thing is to understand how proper document protection will be because if the system is under threat, then watermarks and encryption will not protect data.
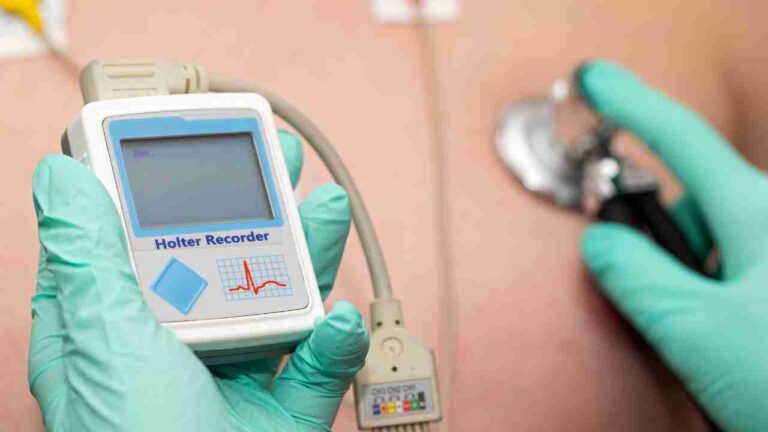
Use Deep Network Traffic Analysis Systems
System protection is a key security and workflow mechanism. Such systems allow you to detect suspicious traffic, which can be an error by internal users or a hacking factor. One of the main advantages of deep analysis systems is real-time protection, which instantly reacts to malware or dangerous tools that can be disguised as ordinary file folders or documents.
This reduces the number of successful hacks or data leaks, ultimately improving the business system and minimizing the damage that hackers or random users can cause.
DDoS Protection
Distributed Denial of Service (DDoS) attacks are the main threat that can disable a company’s server altogether. If you are at least somehow present on the Internet, you can be under the gun of a DDoS attack.
Initially, this method of destabilizing web resources only slightly slowed down the servers, and it was enough to turn it off on your own for a couple of seconds so that the actions of hackers would go to zero. A DDoS attack is carried out from a huge number of computers, which a virus or a data miner most often interconnects.
To protect your workspace or electronic workflow, use various companies’ services or reverse proxy technology. But it’s better not to skimp on protection against DDoS attacks because sometimes this leads to considerable losses in the audience, money, and reputation.
Use Software to Detect Suspicious Files
The effectiveness of a DDoS attack depends on the number of devices and systems that were previously infected with a common kernel (file or program). The reason for the spread of this type of virus is a weak check or, in general, the lack of protection of data or files that get inside the entire system.
Therefore, it is vital to regularly check the system or network architecture for suspicious files and check for new files. Usually, antivirus programs will do this, but sometimes it is worth connecting additional resources because developing antivirus applications increases the level of malware.
Control Access to Electronic Workflow
How many accounts do you have? Maybe 1 or 5. It’s not so important. In any case, a cybercriminal will gain access to the account with weak protection if the protection systems are ineffective.
At best, hackers will get access to a regular account and click and view files. Another thing is when access is available to an account that is not limited in its actions. Then the damage can be quite serious: removing available hosts, creating metrics failure, deleting files, publishing confidential information, etc. Therefore, ensure that there are no unused user accounts in the system and that you use at least two-factor authentication.
Conclusion
The workflow has become safer and more secure with the development of security programs and mechanisms. But over time, hacker approaches to hacking and stealing data is also improving. Any, even minimal protection, can protect important files or personal information.
A secure system allows you to minimize the consequences in the event of a successful attack, and the use of analytics tools allows you to determine the source of the threat. Cyber attacks can and should be resisted.